OpenVPN enables you to create an SSL-based VPN (virtual private network) that supports both site-to-site and client-to-site tunnels. This allows your road warrior users to connect to local resources as if they were in the office, or connect the networks of several geographically distant offices together - all with the added security of encryption protecting your data.
- Recently Windows 10 got updated. After update, the VPN has stopped getting connected. Tried other VPN services but it isnt working. Also deleted and reloaded the VPN app. Nothing seems to be working.
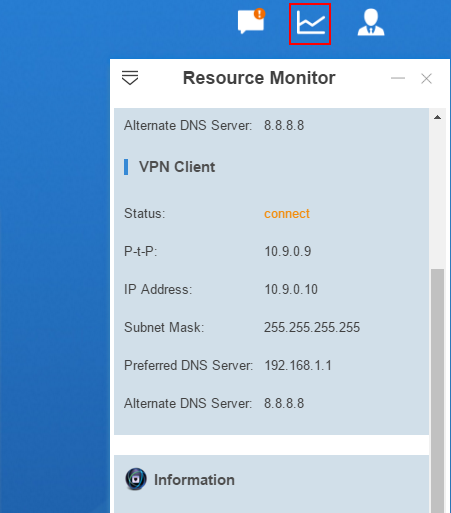
- Assuming one of your client want to secure connection to their server. The client has configured OpenVPN server on their network and provided you client configuration file. In that case you only need to install OpenVPN client application to your system and connect to remote vpn network. This tutorial will help you to install OpenVPN.
- OpenVPN is not just a VPN client but a standard in itself which brings new techniques to create secure end-to-end connections. It’s no surprise that OpenVPN has become a leading security protocol and being implemented in many mainstream VPNs.
This article helps you configure OpenVPN ® Protocol clients. You can also use the Azure VPN Client for Windows 10 to connect via OpenVPN protocol. For more information, see Configure a VPN client for P2S OpenVPN connections.
Before you begin
Create a User VPN (point-to-site) configuration. Make sure that you select 'OpenVPN' for tunnel type. For steps, see Create a P2S configuration for Azure Virtual WAN.
Windows clients
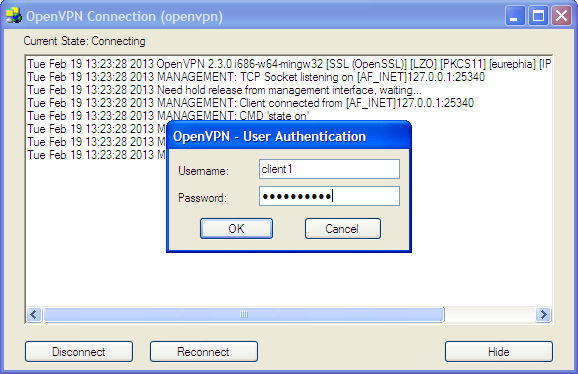
Download and install the OpenVPN client (version 2.4 or higher) from the official OpenVPN website.
Download the VPN client profile package from the Azure portal, or use the 'New-AzVpnClientConfiguration' cmdlet in PowerShell.
Unzip the profile. Next, open the vpnconfig.ovpn configuration file from the OpenVPN folder using Notepad.
Export the point-to-site client certificate you created and uploaded. Use the following article links:
VPN Gateway instructions
Virtual WAN instructions
Extract the private key and the base64 thumbprint from the .pfx. There are multiple ways to do this. Using OpenSSL on your machine is one way. The profileinfo.txt file contains the private key and the thumbprint for the CA and the Client certificate. Be sure to use the thumbprint of the client certificate.
Open profileinfo.txt in Notepad. To get the thumbprint of the client (child) certificate, select the text (including and between)'-----BEGIN CERTIFICATE-----' and '-----END CERTIFICATE-----' for the child certificate and copy it. You can identify the child certificate by looking at the subject=/ line.
Switch to the vpnconfig.ovpn file you opened in Notepad from step 3. Find the section shown below and replace everything between 'cert' and '/cert'.
Open the profileinfo.txt in Notepad. To get the private key, select the text (including and between) '-----BEGIN PRIVATE KEY-----' and '-----END PRIVATE KEY-----' and copy it.
Go back to the vpnconfig.ovpn file in Notepad and find this section. Paste the private key replacing everything between and 'key' and '/key'.
Do not change any other fields. Use the filled in configuration in client input to connect to the VPN.
Copy the vpnconfig.ovpn file to C:Program FilesOpenVPNconfig folder.
Right-click the OpenVPN icon in the system tray and click connect.
Mac clients
Openvpn Client Setup
Download and install an OpenVPN client, such as TunnelBlick.
Download the VPN client profile package from the Azure portal, or use the 'New-AzVpnClientConfiguration' cmdlet in PowerShell.
Unzip the profile. Open the vpnconfig.ovpn configuration file from the OpenVPN folder in a text editor.
Fill in the P2S client certificate section with the P2S client certificate public key in base64. In a PEM formatted certificate, you can open the .cer file and copy over the base64 key between the certificate headers. Use the following article links for information about how to export a certificate to get the encoded public key:
VPN Gateway instructions
Virtual WAN instructions
Fill in the private key section with the P2S client certificate private key in base64. See the Export your private key on the OpenVPN site for information about how to extract a private key.
Do not change any other fields. Use the filled in configuration in client input to connect to the VPN.
Double-click the profile file to create the profile in Tunnelblick.
Launch Tunnelblick from the applications folder.
Click on the Tunnelblick icon in the system tray and pick connect.
Important
Only iOS 11.0 and above and MacOS 10.13 and above are supported with OpenVPN protocol.
iOS clients
Install the OpenVPN client (version 2.4 or higher) from the App store.
Download the VPN client profile package from the Azure portal, or use the 'New-AzVpnClientConfiguration' cmdlet in PowerShell.
Unzip the profile. Open the vpnconfig.ovpn configuration file from the OpenVPN folder in a text editor.
Fill in the P2S client certificate section with the P2S client certificate public key in base64. In a PEM formatted certificate, you can open the .cer file and copy over the base64 key between the certificate headers. Use the following article links for information about how to export a certificate to get the encoded public key:
VPN Gateway instructions
Virtual WAN instructions
Fill in the private key section with the P2S client certificate private key in base64. See Export your private key on the OpenVPN site for information about how to extract a private key.
Do not change any other fields.
E-mail the profile file (.ovpn) to your email account that is configured in the mail app on your iPhone.
Open the e-mail in the mail app on the iPhone, and tap the attached file
Tap on More if you do not see Copy to OpenVPN option
Tap on Copy to OpenVPN
Tap on ADD in the Import Profile page
Tap on ADD in the Imported Profile page
Launch the OpenVPN app and slide the switch in the Profile page right to connect
Linux clients
Open a new Terminal session. You can open a new session by pressing 'Ctrl + Alt + t' at the same time.
Enter the following command to install needed components:
Download the VPN profile for the gateway. This can be done from the Point-to-site configuration tab in the Azure portal.
Export the P2S client certificate you created and uploaded to your P2S configuration on the gateway. Use the following article links:
VPN Gateway instructions
Virtual WAN instructions
Extract the private key and the base64 thumbprint from the .pfx. There are multiple ways to do this. Using OpenSSL on your computer is one way.
The profileinfo.txt file will contain the private key and the thumbprint for the CA, and the Client certificate. Be sure to use the thumbprint of the client certificate.
Open profileinfo.txt in a text editor. To get the thumbprint of the client (child) certificate, select the text including and between '-----BEGIN CERTIFICATE-----' and '-----END CERTIFICATE-----' for the child certificate and copy it. You can identify the child certificate by looking at the subject=/ line.
Open the vpnconfig.ovpn file and find the section shown below. Replace everything between the and 'cert' and '/cert'.
Open the profileinfo.txt in a text editor. To get the private key, select the text including and between '-----BEGIN PRIVATE KEY-----' and '-----END PRIVATE KEY-----' and copy it.
Open the vpnconfig.ovpn file in a text editor and find this section. Paste the private key replacing everything between and 'key' and '/key'.
Do not change any other fields. Use the filled in configuration in client input to connect to the VPN.
To connect using the command line, type the following command:
To connect using the GUI, go to system settings.
Click + to add a new VPN connection.
Under Add VPN, pick Import from file…
Browse to the profile file and double-click or pick Open.
Click Add on the Add VPN window.
You can connect by turning the VPN ON on the Network Settings page, or under the network icon in the system tray.
Next steps

Openvpn Client For Windows
For more information about User VPN (point-to-site), see Create User VPN connections.
Open Vpn Client Linux
'OpenVPN' is a trademark of OpenVPN Inc.